Check security issues detected by GuardDuty, Inspector, and Macie, etc. in AWS Security Hub collectively
awsAWS Security Hub is a service that allows you to collectively check security issues detected by various services
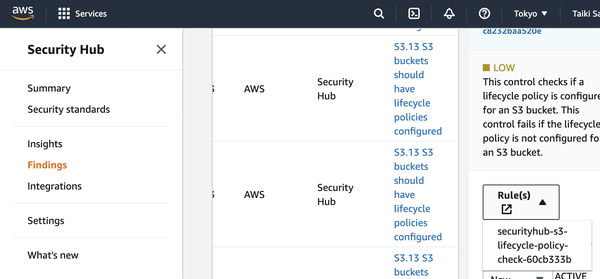
Security standards
Security Hub supports following security standards, and they are enabled, rules are added to AWS Config.
- AWS Foundational Security Best Practices: Best practices for each service
- Center for Internet Security (CIS) AWS Foundations Benchmark: Meet the requirements for certification by the security standardized organization CIS established by the NSA, etc.
- Payment Card Industry Data Security Standard (PCI DSS)
After waiting for a while, the score will be displayed, and you can check each result.
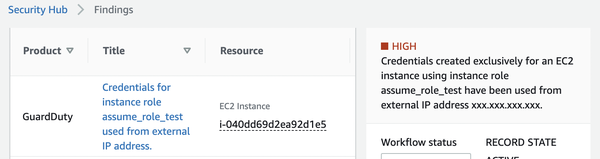
GuardDuty
GuardDuty detects malicious activities with analyzing CloudTrail and VPC flow logs.
For example、once API is called with EC2 credential from local, UnauthorizedAccess:IAMUser/InstanceCredentialExfiltration.OutsideAWS is detected, so you can notice that there is a high possibility that the instance has been invaded through some route.
[ec2-user@ip-172-31-2-24 ~]$ ROLE_NAME=assume_role_test
[ec2-user@ip-172-31-2-24 ~]$ TOKEN=`curl -X PUT "http://169.254.169.254/latest/api/token" -H "X-aws-ec2-metadata-token-ttl-seconds: 21600"`
[ec2-user@ip-172-31-2-24 ~]$ curl -H "X-aws-ec2-metadata-token: $TOKEN" -v http://169.254.169.254/latest/meta-data/iam/security-credentials/$ROLE_NAME
{
"Code" : "Success",
"LastUpdated" : "2022-12-03T06:25:39Z",
"Type" : "AWS-HMAC",
"AccessKeyId" : "ASIAxxxxxxxxxx",
"SecretAccessKey" : "xxxxxxxxxx",
"Token" : "xxxxxxxxxx",
"Expiration" : "2022-12-03T13:01:09Z"
* Closing connection 0
(local)$ % AWS_ACCESS_KEY_ID="ASIAxxxxxxxxxx" AWS_SECRET_ACCESS_KEY="xxxxxxxxxx" AWS_SESSION_TOKEN="xxxxxxxxxx" aws s3 ls <bucket_name>
After that, see /var/log/secure and inspect the history of ssh logins.
[ec2-user@ip-172-31-2-24 ~]$ tail /var/log/secure
Dec 3 08:15:33 ip-172-31-2-24 sshd[1713]: Accepted password for cracker from xxx.xxx.xxx.xxx port 47158 ssh2
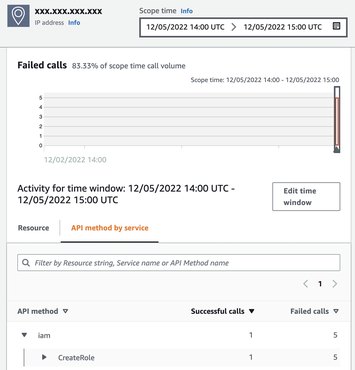
From the “Investigate with Detective” link, moving to Amazon Detective, you can inspect the scope of impact from the IP address and so on. Since there was no S3 object level log that doesn’t appear in CloudTrail’s Event history, it seems necessary to look at Trail logs as well.
Check records of operations for AWS resources with CloudTrail - sambaiz-net
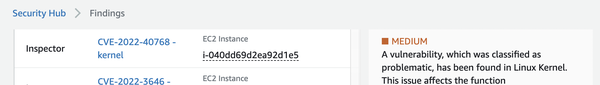
Inspector
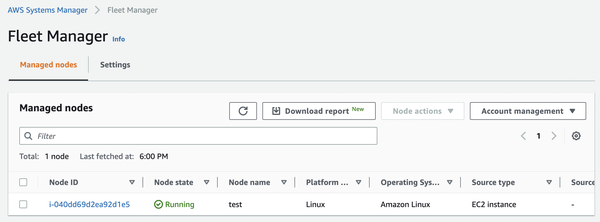
Inspector detects vulnerabilities in EC2 and Lambda, etc.
EC2 instances must be registered in Systems Manager.
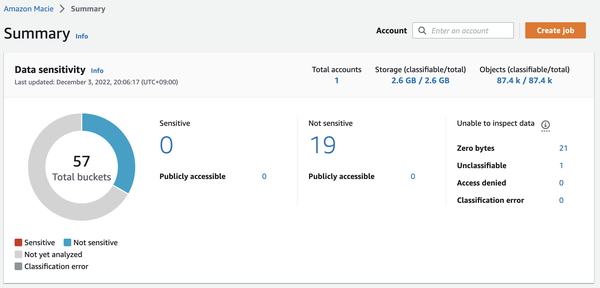
Macie
Macie detects sensitive data in S3.
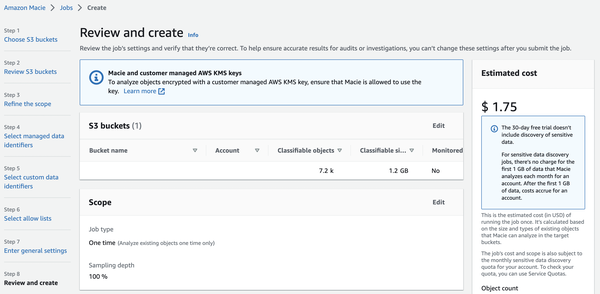
Create a Job by setting Bucket, sampling rate, etc.
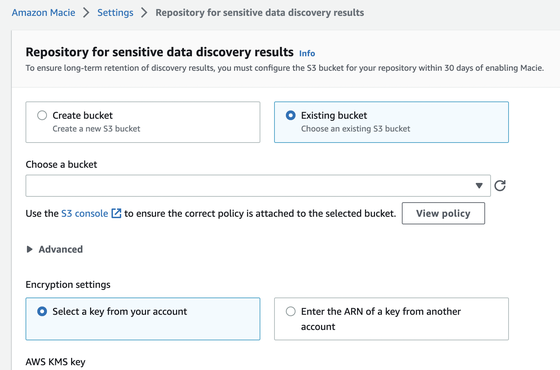
Attach a bucket policy that allows Macie to write encrypted objects to a bucket, and create a KMS key for encryption. After that, setting them and running a job, you can check sensitive data samples.
Settings for querying tables of other accounts with Athena - sambaiz-net
Detected the name in the driver’s copyright.