AWS CloudTrail records AWS API call history, which is used for security auditing and other services such as GuardDuty.
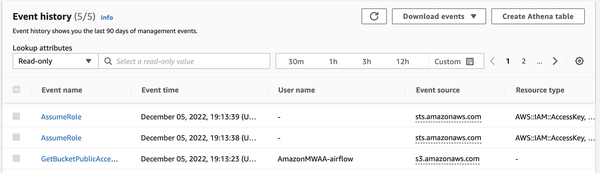
Event history
Event history is recorded per region by default, which is free. The retention period is 90 days, and data events, such as Lambda’s invoke and object-level operations in S3, are not included.
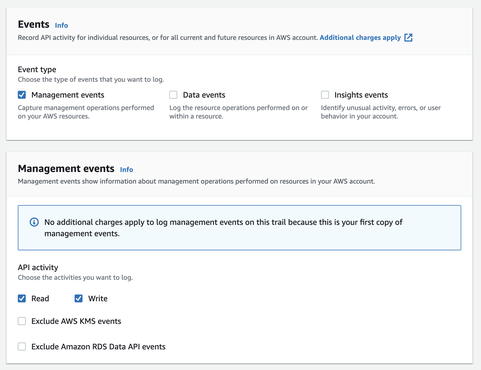
Trails
Creating a trail with selecting the Events to be recorded, logs of all regions are outputted to S3.
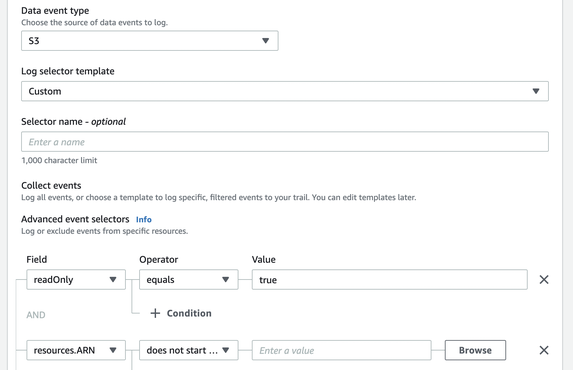
Enabling Data events will incur a charge based on the number of events, but you can filter them by ARN or eventName.
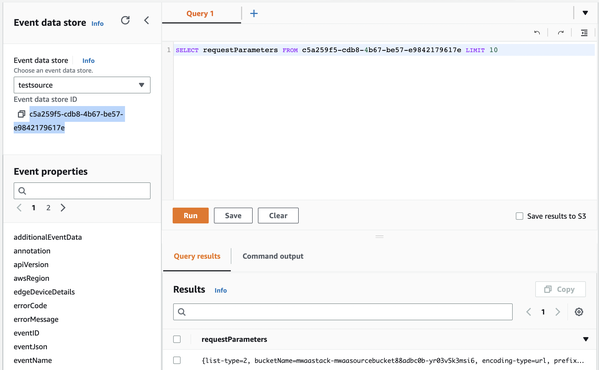
Lake
Once data is ingested into Lake, queries can be executed without creating Athena tables.
Data from AWS Config can now be imported, so you can check it together with Trail logs.